CoCheat Data Leak: US Government Contracts Using Tools Like Cluely to Cheat on Interviews.
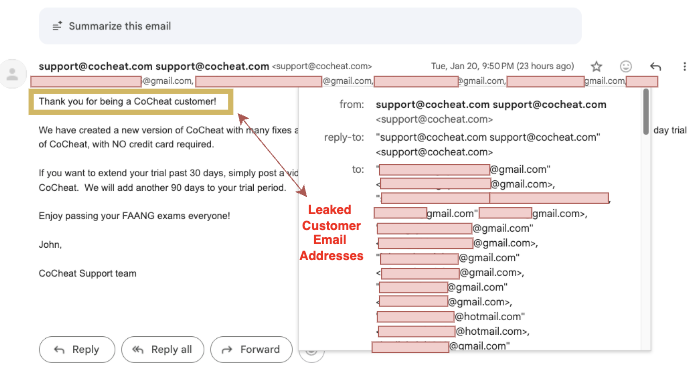
CoCheat is an AI interview assistant (similar to Cluely and InterviewCoder) that helps candidates cheat during virtual interviews. On the night of January 20, 2026, CoCheat accidentally leaked the names and email addresses of its users. The leak happened because instead of BCC’ing a product update email, the company CC’ed it to everyone (classic). That meant the email header exposed the full list of recipients.
Summary of What We Found
- Shockingly: CoCheat users include cybersecurity contractors who work for the US government.
- Unsurprisingly: about 8% of identified CoCheat users work at Fortune 500 companies (including Amazon, Accenture, Oracle, and Cisco).
- Roles ranged from interns to ICs to hiring managers.
- Most were software engineers, followed by AI/ML engineers.
- Most were based in the USA.
- Tiny fraction of users 4% did the smart thing and used disposable emails (example: Proton Mail) when signing up.
Details
How the leak happened
At 10:50pm EST on January 20, CoCheat emailed users a product update. Normally, companies send customer-wide emails using Blind Carbon Copy (BCC), which hides recipients from each other. CoCheat used CC instead, which exposed every recipient email address in the message header—creating a large trove of addresses instantly.
What we did
We reviewed the exposed email addresses to answer basic questions: Who is using CoCheat? Where do they work? Which country are they in?
How we did it
We reverse-searched each email address on Google (we did not use paid reverse-email lookup services). We discarded any address that:
- Google could not confidently associate with a person (73%), or
- Used disposable email services like Proton Mail (4%).
For the remaining 23% where we found a likely match, we double-checked ownership by verifying that a public profile (LinkedIn, GitHub, or a resume) displayed the same email address. We then aggregated the public results.
What We Found
- One CoCheat user appears to be a cybersecurity contractor working with the US government. They used their company email to sign up, which suggests the person may hold a senior role.
- About 8% of identified users work at Fortune 500 companies, including Amazon, Accenture, Lockheed Martin, Oracle, and Cisco.
- Most users: Software engineers.
- Geography trend: USA → India → China → Canada.
Final Words
Being a CoCheat customer does not necessarily prove someone cheated to get a job. But it does signal a trend: more people are adopting these tools. The question becomes: who can we trust? If government contractors and security professionals are using AI cheating tools, what does that imply for the integrity of mission-critical systems they build?
Shameless Plug
CoCheat (and similar AI cheating tools) can be detected with BlindSpꙨts. If you want to see how detection works in your interview flow, book a quick call: